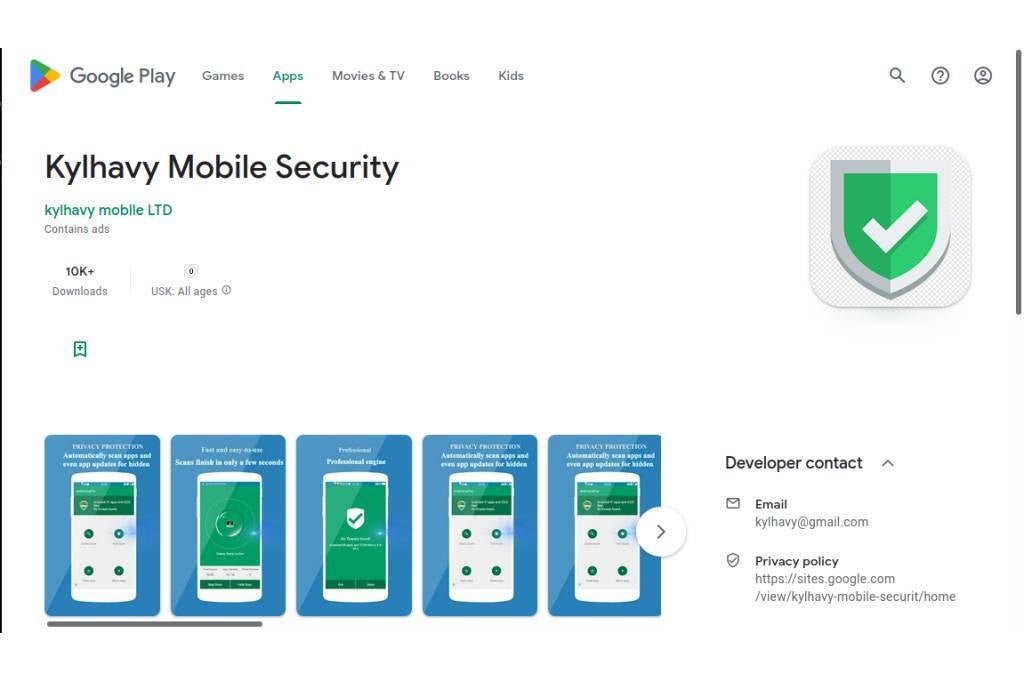
Although these apps are no longer available on the Play Store, users who downloaded them previously must delete them from their phones or risk consequences.
SharkBot dropper apps want to steal banking info
SharkBot was first discovered in late 2021 and the first apps with it were found on the Play Store in March of this year. The mode of operation at that time was to steal information through keylogging, intercepting text messages, tricking users using screen overlay attacks into divulging sensitive info, or giving cyber criminals remote control of the infected device by abusing the Accessibility Services.
They instead ask the command-and-control servers to directly receive the Sharkbot APK file. After that, the dropper apps notify the user of an update and ask them to install the APK and allow the required permissions.
To avoid automated detection, SharkBot saves its hard-coded configuration in encrypted form.
Using the cookie logger, SharkBot siphons off valid session cookies when a user logs into their bank account and sends it to the command-and-control server. Cookies are valuable for threat actors because they help them evade fingerprinting checks and avoid the requirement of user authentication tokens in some instances.
SharkBot seems to be targeting users in Australia, Austria, Germany, Italy, Poland, Spain, the UK, and the US.
The developers are still hard at work improving the malware and Fox-IT expects more campaigns in the future.
To avoid falling prey to such apps, don’t download apps from unknown publishers, especially those that don’t seem to be popular and also go through reviews.

