After a compromise, the first thing investigators will do is review the log files. The default logging on Windows machines, however, does not capture enough information to identify forensic artifacts. You can adjust your logging settings to get enough information to investigate attacks.
First, download and install Sysmon on outward-facing machines. Sysmon remains resident across system reboots to monitor and log system activity to the Windows event log. It provides detailed information about process creations, network connections, and changes to file creation time.
You can tweak Sysmon as noted in the Sysmon cheat sheet to optimize its use, specifically around monitoring events that are a sign of malicious activity. GitHub offers additional resources on Sysmon.
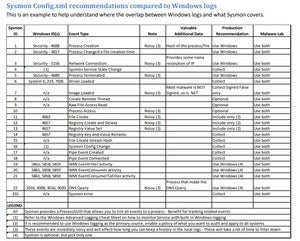 MalwareArchaeology
MalwareArchaeologySysmon configuration guidance

